Do you offer two factor / dual factor authentication?
Yes, we offer two factor (2FA) or dual factor authentication for logging into our cloud management panel. This is a feature that must be enabled company-wide (for all users). It is not possible to enable it for one user and not another because that could create a back-door.
2FA supports the following methods:
- One time code sent via Text Message/SMS
- One time code sent via email
- DUO Mobile app (multiple methods)
- TOTP (Time Based One Time Password)
- E.G. Google Authenticator app for Android or iPhone & iPad
- LastPass Authenticator
- Authy
- DUO Mobile TOTP
- many others…
Configuring 2FA
In order for the users in your account to utilize 2FA, you first need to configure it for the company. To do this, click the gear/cog icon in the upper-right corner of the panel, and then go to the Company sub-tab. There you will see your company in the table. Double click it, or select it once and click “edit” on the toolbar to open the dialog.
Within the company dialog, you will see the 2F Authentication section and a “configure” button as shown below.
![]()
Note: If you do not see the button or the company tab, then you may not have sufficient permissions. Contact your company administrator for access.
When you click the Configure button, you will be presented with a dialog allowing you to select one or more 2FA options to present to your users. It will look like this:
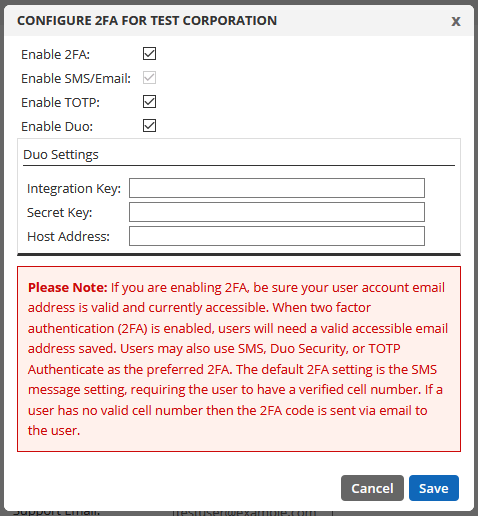
Checking “Enable 2FA” will reveal the various options. By default, SMS/Email support will be enabled since the email code is the default fall-back method for all users. The moment you click “save” in this dialog, 2FA will be enabled for all users by default (including API users, see our note below about those). Users with a valid mobile number will receive an SMS, and users without a valid mobile number will receive an email. They will then see a dialog like this the next time they log in:
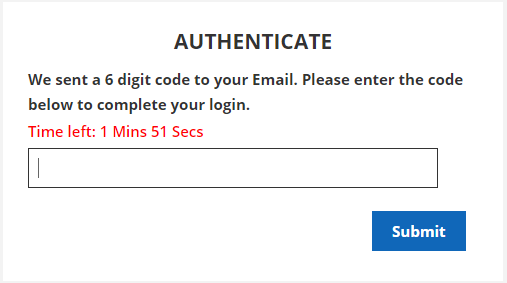
The user will have 2 minutes to enter the 6 digit code received via email or SMS after successfully entering their email and password in order to complete the login process, otherwise they will have to request a new code to try again.
You may also enable TOTP and DUO for your users. If you enable DUO, you will need to have an account with them and you will be required to enter your Integration Key, Secret Key and Host Address from your account. You can signup for a free 10 user account with DUO here. NOTE: To obtain the Integration Key, Secret Key and Host Address from your DUO account, select the generic application called “Auth API” from their list of applications.
Your users can choose their preferred 2FA
Once you have selected the options you would like to present to your users, there are two ways to enable per-user.
- Doing it for them: You can go to the “Users” sub-tab and edit each user individually. Within the user dialog you will see a similar “Configure” button for each user. There you can activate SMS/Email, your favorite TOTP app or DUO. Note: You may need their mobile device to complete this on their behalf.
- Self Service: The next time your users log in (and successfully pass the built-in email or SMS 2FA) they can click the padlock icon in the upper-right corner of the panel to modify their 2FA settings. They will see a section for choosing their preferred 2FA type, as shown below:
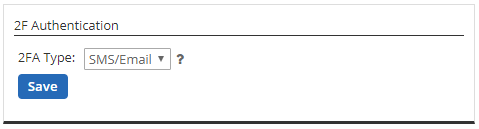
By default, the SMS/Email option is chosen. And, as mentioned above, if they have a valid cell/mobile number in their user profile, they will receive a 6 digit one time code via SMS to complete their login. If they do not have a valid mobile number in their user profile, they will receive the 6 digit code via email.
TOTP
If the user chooses “TOTP” from the drop-down menu, they will be presented with the options to configure it as shown below:
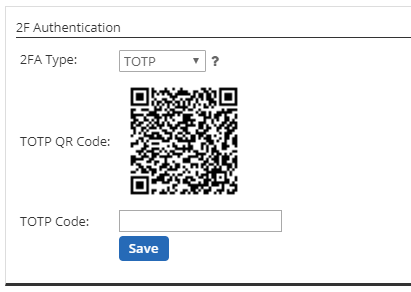
The user must download their favorite TOTP App such as Google Authenticator app for Android or iPhone/iPad or Authy etc. or have it already installed. Within the app, the user will click to “Add an account” and scan the barcode shown on the screen. When successfully scanned, enter the 6 digit code (without spaces) into the “TOTP Code” box and click save. Don’t forget to rename the new account on your mobile device to Total Uptime, especially if you use a TOTP Authenticator app already and have more than one entry configured.
That’s it! When the user logs in the next time, they will be prompted to enter a 6 digit code from the app on their device. This code is time-based and changes frequently, so be certain to enter it within 2 minutes.
DUO
If the user chooses “Duo” from the drop-down menu, they will see a DUO Setup button as shown below:

Clicking the button will open a new tab or browser window to complete the process. You MUST already have an active and authenticated mobile device on your company DUO account before proceeding to register. This process will vary by company policy (if established). For example, if the email matches an existing DUO account within your organization, the setup may be quite simple. However, with the free DUO account or trial account, it will generally ask you for your mobile number first so it can send you the download link, or if you already have the DUO mobile app, it will phone you with an activation code.
If you need more specific guidance configuring DUO, check out this article: Enabling DUO with Total Uptime
Caution: API Accounts
What happens if you have created a user for accessing our API? Clearly 2FA will break that connection, so to continue using an account for API access after turning 2FA on for your company, edit your API user account and check the “API Account” checkbox at the bottom of the dialog. Make sure your API password is very strong, and also ensure that the role is specifically configured to only permit the actions you use. This will ensure the greatest security for your account.
Of course, if you have any challenges configuring 2FA for your account or your users, do not hesitate to contact us. We’re always here to help!
Other keywords: 2-factor, 2 factor, dual-factor, two-factor, multi-factor, 2FA, OTP, TOTP