Protect your organization against malware, phishing, botnets and more with Protective DNS
Total Uptime’s Protective DNS (PDNS) service enhances your internal corporate DNS by implementing policy-based filtering that detects malicious domains such as botnets, command and control servers, protects against malware and phishing and allows you to block undesirable content with granular category controls.
Protective DNS For SMB and Enterprise
Whether you’re a Fortune 500 organization or a small business, Total Uptime Protective DNS provides Enterprise grade protection and filtering for your users. Protect your organization from costly phishing or ransomware attacks and stop infections before they happen. Our global anycast network means we scale for even the largest global businesses.
- Protect 10 to 100k+ users
- Manage different networks separately
- Easy-to-use Control Panel
- API Integration Available

Protective DNS For Government
Due to the centrality of DNS for cybersecurity, the Department of Defense (DoD) included DNS filtering as a requirement in its Cybersecurity Maturity Model Certification (CMMC) standard (SC.3.192). The Cybersecurity and Infrastructure Security Agency issued a memo and directive requiring U.S. government organizations to take steps to mitigate related DNS issues. Total Uptime Protective DNS meets all 11 capabilities listed in the NSA and CISA document entitled “Selecting a Protective DNS Service”.
Learn More
Protective DNS For Education
DNS Resolution helps University and K-12 networks to be CIPA compliant and protect students and staff from inappropriate websites and malicious domains. We can accommodate institutions of any size and offer attractive Education pricing.
- Separate policies for faculty vs. students
- Guest Wifi network control
- Easy-to-use Control Panel

Total Uptime Protective DNS is superior cyber threat protection at the gateway.
Everyday across the network, we block more than 1 million deceptive sites. The average cost of a security breach is more than $3.86M. This includes hard costs like paying ransoms and shoring up security, but also lost productivity due to system lockouts, and the cost of crisis communications and reputation rebuilding. Can your business afford a cybersecurity incident?
Powered by Artificial Intelligence (AI)
AI Kills Malware, Detects Phishing Attacks and more!
Our competitors rely on static, human categorized databases that are often weeks or months out of date. Millions of domains are registered or re-directed each day, meaning they allow you to access many domains that are malicious as they are not present or out of date within their database.
Rather than bragging about a large, out of date database, we use our machine learning algorithms to analyze unknown domains on the fly and constantly keep our data up-to-date. This means you can rest assured that you’re protected with the most up to date threat and domain analysis in the industry.
Protection From Malware and C&C Servers
Malware can spread through forced downloads or malicious ad content.
It includes viruses, worms, spyware, ransomware, and trojan horses. The most common way that malware gets onto a computer or other device is through surfing hacked sites. So the best way to protect your company from malware is to prevent your users from ever accessing these sites. Protective DNS from Total Uptime does just that!
Protection From Ransomware
Ransomware is software that allows hackers to encrypt files, networks, and computers remotely.
Hackers then hold your data hostage until your company pays a ransom. With the evolution of ransomware in key sectors like healthcare as well as the ubiquity that Ransomware-As-A-Service offers, this threat technique has become one of the top causes of cybersecurity incidents worldwide.
The key to ransomware protection is stopping malware from being downloaded in the first place, which usually requires blocking the site that hosts the malicious content before an unsuspecting user can visit it and become infected.
Protection From Phishing Attacks
Phishing and spear phishing attacks are a favorite among hackers because they are relatively easy to implement.
They use email or chat (such as public Slack channels or Discord) to lure victims into a scam, or more commonly to a link where they will enter data or download malware. Phishing attacks can be broad and general, impersonating institutions like banks or hospitals, or they can be targeted and sophisticated, often impersonating employees inside your own organization. Because Protective DNS is constantly scanning the web for new malicious sites, we can prevent phishing attacks by protecting your employees before they hit a malicious site or give a phisher their data.
Protection From Cryptojacking
A true 21st century threat, cryptojacking is the unauthorized takeover of a computer or network to “mine” cryptocurrency.
Because new currency is created by computers using massive amounts of computing resources computational bandwidth is at a premium. Cryptojacking infects a distributed network of computers to utilize their computational bandwidth, slowing down the device and, at scale, driving up your energy costs. Total Uptime Protective DNS has a robust catalog of known cryptojacking sites and domains that contain cryptocurrency references can be blocked in a single click.
Protection from Generated and Typo Domains
Thousands of people type Amazan.com into their browser every day. Turns out, the average internet user isn’t always the best speller. Bad actors take advantage of this by setting up malicious sites with domain names that feature common misspellings of familiar sites. Every day we seem to discover new “Chase” login pages with an increasingly creative variety of typos. Protective DNS shields the user from typosquatting by blocking access to domains that are known to contain malware or malicious content. Never worry about misspelled domain names again.
Protection for Off-Network Users & Clients
You can prevent access to unwanted and malicious content on all devices, on and off your network.
Our protective DNS Roaming Clients for Windows, Mac, iOS, Android and ChromeOS give you enhanced control, visibility, and reporting of all the devices in use by your organization. You never have to worry about installing patches, because your filtering policies are stored in the cloud.

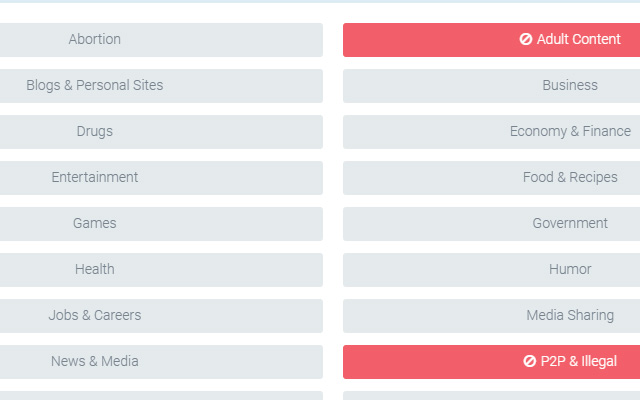
Web Content Filtering with Category Blocking
Deploy comprehensive and customizable URL and internet content filtering policies in mere minutes.
Simply tell Protective DNS what categories of websites you want to block – Adult Content, Illegal Content, Streaming Media, Chat & Instant Messaging, Social Networking, etc. – and we’ll do the rest. Our proprietary algorithms intelligently categorize sites so you don’t have to constantly maintain a list of domains.
You can even enforce search engine SafeSearch for Google, Bing, DuckDuckGo and others, YouTube restricted modes, and filtering avoidance domains so nothing slips through the cracks.
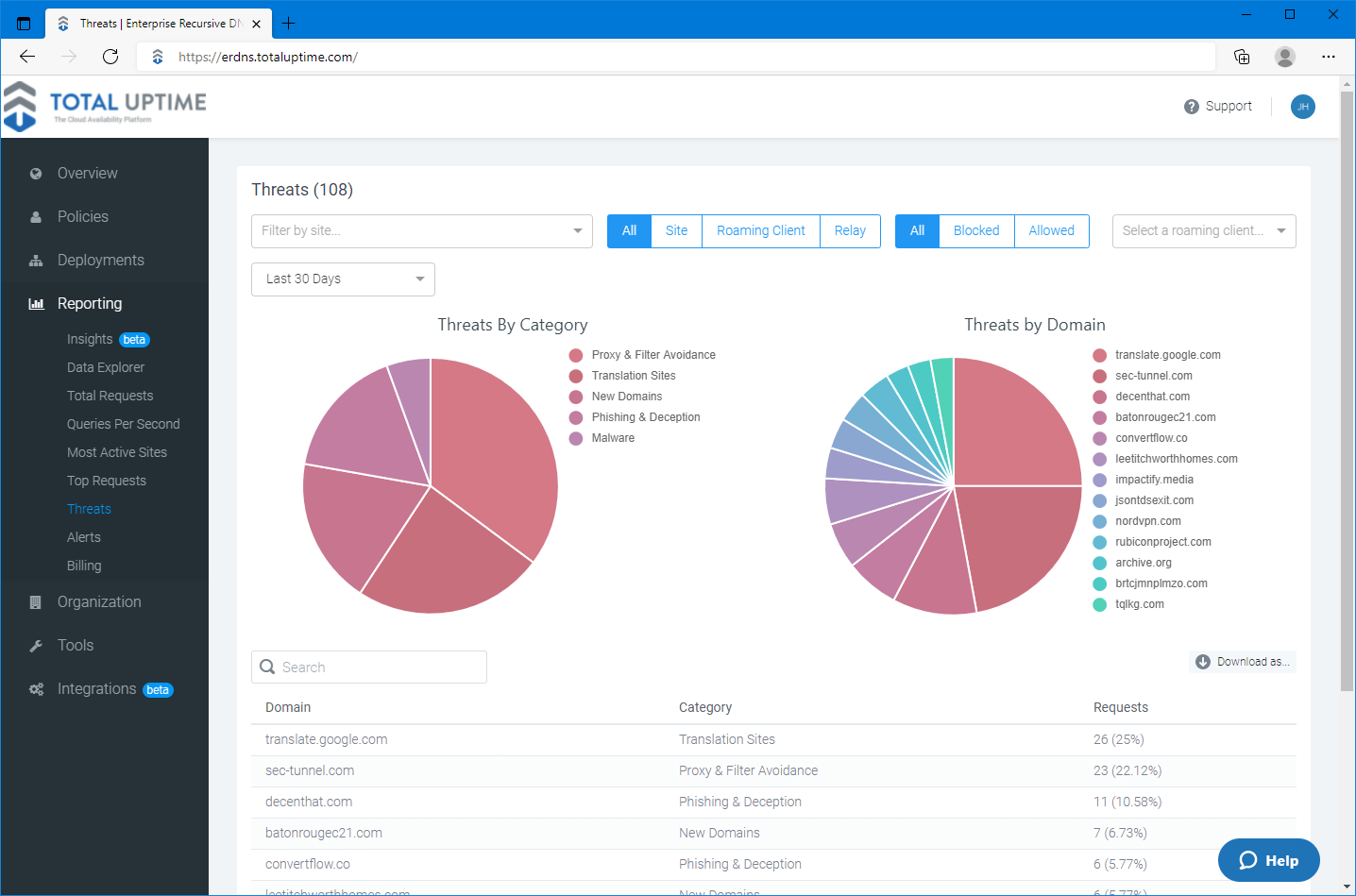
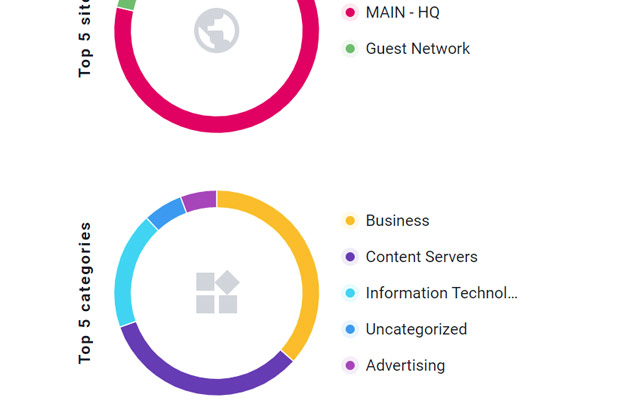
Comprehensive DNS Reporting
From an overview to the fine details of your network traffic and security, our easy-to-use analytics and reports allow you to clearly visualize usage patterns and top destinations across all of your networks.
Activity Reports – Get details and trends for total requests, queries per second, most active networks, and top requests.
Security Threats Report – Quantify the level of protection you’re delivering to your networks and identify the source and frequency of attacks against your networks.
Query Log – Full query log data for troubleshooting investigation, streaming in real time.
World-Class Support
Total Uptime is extremely customer focused. Our US-Based support team prides themselves on being easy to work with and extremely responsive. We’re here when you need us from help with a simple configuration change to something more complex, like a custom implementation.
"The reliability and support provided by Total Uptime is exactly what Thru was looking for." - Kevin Westenkirchner, Vice President, Operations - Thru.






