What Is Load Balancing — And Do I Need It?
Unless your job encompasses application availability or delivery, you may not be aware of what load balancing is, what it does, or whether it is even a necessary component. As to the last part of that statement, the answer is simple: It is absolutely necessary. In today’s demanding online world, load balancing helps to ensure many things including application availability and performance. For a computer network, load balancing is as normal and natural as breathing is for humans. It’s a way for data traffic load to quickly tap into the hardware and software resources that will enable it to successfully complete its operation. Read on to learn more.
What is Load Balancing?
In our article, Cloud Load Balancing 101, we discuss the difference between traditional network-based load balancing and global cloud load balancing. The following diagram from that article gives a clear visual representation of how load balancing — in its original form, at least — uses traditional appliances to distribute traffic from internet users to multiple devices or servers within the data center.
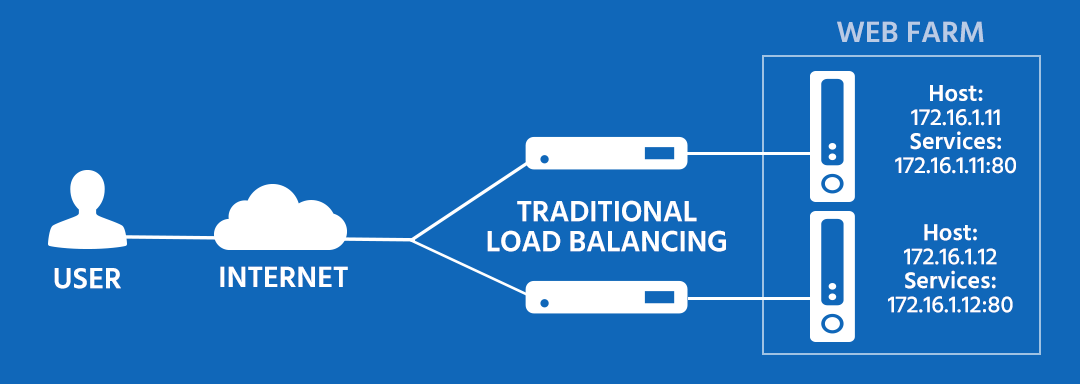
Notice how in this implementation, designated hardware is represented by the various icons. But times have changed. We no longer need to be tethered to dedicated equipment. Today’s networks are replete with virtualized servers, routers, switches, and other devices. The cloud has left behind the constraints of physical equipment and now embraces the dynamics of a software-based infrastructure.
Modern networking now includes the common use of a new concept and term called application delivery. Rather than asking “what is load balancing?”, the better question might be “what is application delivery networking?”
Modern networking now includes the common use of a new concept and term called application delivery. Rather than asking “what is load balancing?”, the better question might be “what is application delivery networking?” That’s because IT centric organizations these days are less focused on equipment and more concerned with the successful delivery of applications.
So while load balancing has always been about distributing load across multiple devices, the term has evolved to encompass a whole range of application-centric controls and processes to ensure the optimized transmission of network traffic. Major vendors like F5, Citrix, A10 and others use something called an Application Delivery Controller (ADC) for this work. In a whitepaper, F5 writes, “Key network and application functions, such as load balancing, encryption, acceleration, and security, can be provided via Application Delivery Controllers (ADC), which are physical or virtual appliances functioning as proxies for physical servers.” But the problem with this concept is that IT buyers are still forced to buy hardware or software to obtain the benefits these devices have to offer. These major vendors are hardware and software companies at their core, and do not know how to provide their product in any other way but as hardware or software, which is clearly no longer in the best interest of today’s IT centric organizations. At Total Uptime, we understand today’s needs and our model clearly reflects that.
Application Delivery in the Cloud
The edge application delivery services offered by Total Uptime are now completely removed from the local data center and instead pushed to the very edge of the internet. Businesses who once turned ADC appliance vendors for onsite hardware and software solutions now turn to Total Uptime for even more control over application delivery in the cloud. Edge application delivery includes a robust cloud load balancer that gives you complete control over network traffic on the internet before it reaches your devices. It can be used for load balancing, disaster recovery, failover, acceleration, firewalling and security as well cloud integration between on-premise and cloud environments.
Cloud load balancing is not quite the same as the simple two-device traffic sharing solution of bygone days, like we depicted above, although it can provide this basic level of service with ease. We wrote about the transition in our article Load Balancing Moves to the Cloud. We can route traffic no matter the source or destination, locally or across the globe.
Redundancy is extremely important in networking, and it works very closely together with load balancing. When one device fails, another takes over. Meanwhile, in times of high traffic, the backup or redundant, device can function as a load balancer. In cloud computing, ensuring application delivery often means setting up alternate paths and resources to keep everything online all the time. And load balancing means your applications can be delivered optimally even in times of peak traffic.
Do I Really Need Load Balancing?
You might be surprised to know you’re already using it every day. Think of all the web services that you use. Email, social media, news websites, podcasts, video sites, banking — all of these services load balance their traffic. They would be foolish not to because the risks associated with a single-point-of-failure are too great, but more importantly, no single device could handle the load anyway. But these organizations go much further than that. They use full application delivery platforms to not only ensure availability, but the performance and security of their applications as well.
If you happen to be creating a new web service yourself, and you are wondering whether you should load balance it, the answer is yes. You may think that your service is too small or unimportant for this kind of extra treatment. But you shouldn’t think that way. Load balancing, like redundancy, should be standard for any web service. It is far better and often similar in cost to deploy an application or service on two smaller pieces of hardware than one larger. The risks of poor performance are right up there with your concerns about downtime. All it takes is one incident of peak traffic when your service protocols are overworked for you to lose a customer.
Think of it this way. If you go to a website and it’s too slow to use, what do you do? In the 21st century, our patience has worn quite thin. We don’t like to wait. You’ll go somewhere else and probably won’t try to use that service anymore. In fact, there are numerous statistics out there that confirm that when a site takes longer than 1 second to load, users start dropping off for competitors very quickly. Load balancing can prevent these kinds of problems.
Conclusion
What is load balancing, you ask? It is the very thing that keeps the internet performing well after 30 years. Everyone knows the importance of maintaining equilibrium and balance in all areas of life. Without load balancing, your IT infrastructure will never function properly. On the other hand, Total Uptime’s Edge Application Delivery platform can optimize the availability and performance of your network. We encourage you not only to commit to load balancing throughout your network, but also take advantage of the best load balancing — and application delivery — services on the market.
 What is an Application Delivery Network?
What is an Application Delivery Network?  Global Server Load Balancing (GSLB)
Global Server Load Balancing (GSLB)  Measuring Failure
Measuring Failure